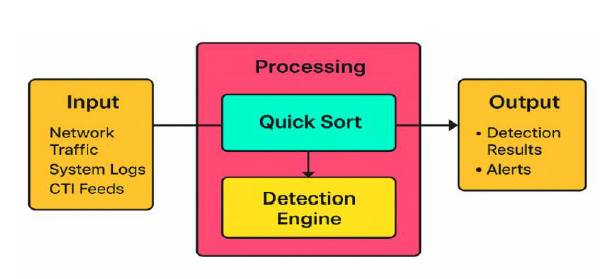
A QUICK SORT–BASED FRAMEWORK FOR EFFICIENT THREAT LOG ANALYSIS AND PRIORITIZATION IN CYBERSECURITY SYSTEMS
DOI:
https://doi.org/10.33003/fjs-2026-1002-4289Keywords:
Quick Sort, Cybersecurity Framework, Data Ordering, Intrusion Detection, Algorithm Optimization, Computational Efficiency, Threat Intelligence, Sorting AlgorithmsAbstract
The exponential growth of digital data and the increasing sophistication of cyberattacks have heightened the demand for high-performance cybersecurity frameworks capable of processing and analyzing large-scale datasets efficiently. Traditional research in cybersecurity has largely emphasized the development of advanced detection models and encryption schemes, often overlooking the computational efficiency of data preprocessing, a critical stage that influences detection latency and accuracy. This study presents the Quick Sort–Cybersecurity Framework (QS-CF), an innovative integration of the Quick Sort algorithm into the preprocessing pipeline of cybersecurity analytics systems. The framework leverages algorithmic data ordering to enhance computational throughput and improve real-time intrusion detection efficiency. Using simulated network traffic datasets, the QS-CF achieved a 25% reduction in sorting time, a 1.3× increase in throughput, and a 12% improvement in detection accuracy compared to existing frameworks utilizing Merge and Insertion Sort algorithms. The results demonstrate that classical algorithmic optimizations, when strategically embedded in cybersecurity workflows, can substantially improve system responsiveness, reduce false alerts, and support scalable threat intelligence operations. The QS-CF offers a lightweight, adaptable, and cost-effective model for optimizing security system performance, providing a foundation for future research into privacy-preserving, distributed, and AI-augmented cybersecurity solutions.
References
Ala’Anzy, M. A., Mazhit, Z., Ala’Anzy, A. F., Algarni, A., Akhmedov, R., & Bauyrzhan, A. (2024). Comparative Analysis of Sorting Algorithms: A Review. 2024 11th International Conference on Soft Computing & Machine Intelligence (ISCMI), 88–100. https://doi.org/10.1109/iscmi63661.2024.10851593
Chethan , H. N. (2017). Network Intrusion dataset(CIC-IDS- 2017). Kaggle.com. https://www.kaggle.com/datasets/chethuhn/network-intrusion-dataset
Deshmukh, P., & Carter, B. (2023). Secure Multi-Party Computation Protocols for Privacy-Preserving Data Analysis. International Journal of Recent Advances in Engineering and Technology, 12(2), 1–6. https://journals.mriindia.com/index.php/ijraet/article/view/120
Diana, L., Dini, P., & Paolini, D. (2025). Overview on Intrusion Detection Systems for Computers Networking Security. Computers, 14(3), 87. https://doi.org/10.3390/computers14030087
Gu, T., Wang, Y., Cloud, A., Tinoco, A., Shi, E., Chen, B., & Yi, K. (2025). Flexway O-Sort: Enclave-Friendly and Optimal Oblivious Sorting Flexway O-Sort: Enclave-Friendly and Optimal Oblivious Sorting. https://www.usenix.org/system/files/usenixsecurity25-gu-tianyao.pdf
Gu, T., Wang, Y., Tinoco, A., Chen, B., Yi, K., & Shi, E. (2023). Flexway O-Sort: Enclave-Friendly and Optimal Oblivious Sorting. Cryptology EPrint Archive. https://eprint.iacr.org/2023/1258
Haseeb-ur-rehman, R. M. A., Aman, A. H. M., Hasan, M. K., Ariffin, K. A. Z., Namoun, A., Tufail, A., & Kim, K.-H. (2023). High-Speed Network DDoS Attack Detection: A Survey. Sensors, 23(15), 6850. https://doi.org/10.3390/s23156850
Jia, W., Sun, M., Lian, J., & Hou, S. (2022). Feature Dimensionality reduction: a Review. Complex & Intelligent Systems, 8, 2663–2693. https://doi.org/10.1007/s40747-021-00637-x
Jose, J., & Jose, D. V. (2019). Impact of Distributed Denial of Service attack in Internet of Things Applications-An Overview. ResearchGate, 28(17), 201–205. https://www.researchgate.net/publication/378315828_Impact_of_Distributed_Denial_of_Service_attack_in_Internet_of_Things_Applications-An_Overview
Khalil, A., & Abu-Naser, S. S. (2025, June 6). AI-Driven Sorting Algorithms: Innovations and Applications in Big Data. https://doi.org/10.13140/RG.2.2.19176.74245
Lima, M. G., Carvalho, A., Gabriel, Á. J., Escouper, C., & Goldschmidt, R. R. (2024). Impacts of Data Preprocessing and Hyperparameter Optimization on the Performance of Machine Learning Models Applied to Intrusion Detection Systems. ArXiv.org. https://arxiv.org/abs/2407.11105
Maithri Bairy, Pai, P., Kini, N. G., & K. Jyothi Upadhya. (2025). Parallelized Hybrid Sorting Using Quick and Insertion Sort for Big Data. Lecture Notes in Electrical Engineering, 503–513. https://doi.org/10.1007/978-981-96-9203-3_41
Merlano, C. (2024). Enhancing Cyber Security through Artificial Intelligence and Machine Learning: A Literature Review. Journal of Cyber Security, 6(1), 89–116. https://doi.org/10.32604/jcs.2024.056164
Mohamed, N. (2025). Artificial intelligence and machine learning in cybersecurity: a deep dive into state-of-the-art techniques and future paradigms. Knowledge and Information Systems, 67, 6969–7055. https://doi.org/10.1007/s10115-025-02429-y
Mohammad Kamrul Hasan, Rabiu Aliyu Abdulkadir, Islam, S., Thippa Reddy Gadekallu, & Nurhizam Safie. (2024). A review on machine learning techniques for secured cyber-physical systems in smart grid networks. Energy Reports, 11, 1268–1290. https://doi.org/10.1016/j.egyr.2023.12.040
Munappy, A. R., Bosch, J., Olsson, H. H., Arpteg, A., & Brinne, B. (2022). Data management for production quality deep learning models: Challenges and solutions. Journal of Systems and Software, 191, 111359. https://doi.org/10.1016/j.jss.2022.111359
Nagi. (2025). NSL-KDD Dataset (filtered version of KDD). Kaggle.com. https://www.kaggle.com/datasets/primus11/nsl-kdd-dataset-filtered-version-of-kdd
Rao, C. K., Singh, K., & Kumar, A. (2021). Oblivious stable sorting protocol and oblivious binary search protocol for secure multi-party computation. Journal of High Speed Networks, 27(1), 67–82. https://doi.org/10.3233/jhs-210652
Santos, P., Abreu, R., Reis, M. J. C. S., Serôdio, C., & Branco, F. (2025). A Systematic Review of Cyber Threat Intelligence: The Effectiveness of Technologies, Strategies, and Collaborations in Combating Modern Threats. Sensors, 25(14), 4272. https://doi.org/10.3390/s25144272
wenbosun703. (2025). Flexway O-Sort Enclave-Friendly and Optimal Oblivious Sorting. Scribd. https://www.scribd.com/document/944603571/Flexway-O-Sort-Enclave-Friendly-and-Optimal-Oblivious-Sorting
Downloads
Published
Issue
Section
Categories
License
Copyright (c) 2026 Oluwakemi Sade Ayodele, Juliet Chioma Odiketa, Folashade Olumodeji Auru, Ayomide Lewis Seyi-Ayodele

This work is licensed under a Creative Commons Attribution 4.0 International License.