A SYSTEMATIC STUDY OF CYBERSECURITY MESH ARCHITECTURE
DOI:
https://doi.org/10.33003/fjs-2026-1005-4969Keywords:
Cybersecurity Mesh Architecture, Organizations, Security, Perimeter, Implementation, Challenges, FrameworkAbstract
In recent times, technological advancements—spanning across decentralized devices, cloud platforms, widespread Internet of Things (IOT) ecosystems—have rendered traditional perimeter-centric defense systems insufficient, and this has drawn much attention. In response, Cybersecurity Mesh Architecture (CSMA) emerges as the essential framework for securing modern, distributed environments, by providing organizations with a strategic edge in protecting their digital transformation efforts. To better understand this trend, this study systematically reviews developments in CSMA researches, drawing insights from previous literatures. It examines the architecture’s core components and practical implementations. Additionally, organizations benefit from increased operational efficiency through security automation, critical infrastructure and extended enterprise ecosystems. The study presents a conceptual model of CSMA and critically evaluates recent scholarly works that address its application, integration challenges (notably with legacy systems), and risk mitigation strategies. It highlights key unresolved issues and research challenges that need to be addressed to strengthen cyber security. Ultimately, this study examines CSMA’s growing significance as a strategic solution in today’s dynamic and challenging threat environment and its ability to transform cybersecurity practices in digitally evolving organizations. Findings indicate that the adoption of CSMA yields significant improvements in organizational security performance. Across multiple studies, CSMA is associated with enhanced threat detection capabilities, faster incident response times, and more consistent policy enforcement. Empirical evidence further demonstrates that when integrated with advanced techniques such as edge computing and adaptive policy mechanisms, CSMA contributes to higher detection accuracy, reduced response latency, and lower false-positive rates.
References
Abuzied Y. et al. (2024). A privacy-preserving federated learning framework for blockchain networks. Cluster Computing, vol 27, pp 3997 - 4014. doi:https://doi.org/10.1007/s10586-024-04273-1
Adaptive Zero Trust Policy Management Framework in 5G Network. (2025). Mathematics: Application of Artificial Intelligence in Decision Making, vol 13(9). doi:https://doi.org/10.3390/math13091501
Adaptive Zero Trust Policy Management Framework in 5G Networks. (2025). Mathematics: Application of Artificial Intelligence in Decision Making, vol 13(9). doi: https://doi.org/10.3390/math13091501
Aishwarya R. et al. (2025). CSMA: Cyber Security for Mobile Applications using Artificial Intelligence. 2025 International Conference on Intelligent and Cloud Computing (ICoICC), pp. 1-6. doi:https://doi.org/10.1109/ICoICC64033.2025.11052002
Alnaim K. A. & Alwakeel A. M. (2025). Zero Trust Strategies for Cyber-Physical Systems in 6G Networks. Mathematics: Application of Artificial Intelligence in Decion Making, vol 13(7). doi: https://doi.org/10.3390/math13071108
Arif T. et al. (2025). A Comprehensive Survey of Privacy-Enhancing and Trust-Centric Cloud-Native Security Techniques Against Cyber Threats. Sensors, vol 25(2350), pages 1-30. doi: https://doi.org/10.3390/s25082350
Arif T. et al. (2025). A Comprehensive Survey of Privacy-Enhancing and Trust-Centric Cloud-Native Security Techniques Against Cyber Threats. Sensors, vol 25(2350), pp 1-30. doi: https://doi.org/10.3390/s25082350
Asad M. & Otoum S. (2024). Integrative Federated Learning and Zero-Trust Approach for Secure Wireless Communications. IEEE Wireless Communications, vol 31(2), pp 14-20. doi: https://doi.org/10.1109/MWC.001.2300355
Attkan A. & Ranga V. (2022). Cyber-physical security for IoT networks: a comprehensive review on traditional, blockchain and artificial intelligence based key-security. Complex & Intelligent Systems, vol 8, pp. 3559 - 3591. doi:https://doi.org/10.1007/s40747-022-00667-z
Bishop M. (2004). Introduction to Cyber Security. Addison-Wesley Professional. Retrieved June 29th, 2025
BMJ. (2021). PRISMA 2020 explanation and elaboration: updated guidance and exemplars for reporting systematic reviews. 372(160). doi: https://doi.org/10.1136/bmj.n160
Chen F. et al. (2021). IoT Cloud Security Review: A Case Study Approach Using Emerging Consumer-oriented Applications. ACM Computing Survers, vol 54,4, Article No. 75, pages 1 - 26. doi: https://doi.org/10.1145/3447625
Chen F. et al. (n.d.). IoT Cloud Security Review: A Case Study Approach Using Emerging Consumer-Oriented Applications. ACM Computing Surveys, vol 54(4)(article 75), 2021. doi: https://doi.org/10.1145/3447625
Cisco. (2022, November 21). Cisco Solutions. Retrieved June 24, 2025, from Securing Cloud-Native Applications - Azure Design Guide: https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/scloud-azure-cn-design-guide.html
Cruz B. R. et al. (2024). The cybersecurity mesh: A comprehensive survey of involved artificial intelligence methods, cryptographic protocols and challenges for future research. Neurocomputing, vol 581(127427), pp. 1-33. doi: https://doi.org/10.1016/j.neucom.2024.127427
Dhillon P. (2022, July 06). How to write a good scientific review article. The FEBS Journal, vol 289(13), pp. 3592-3602. doi: https://doi.org/10.1111/febs.16565
Dindigala R. & Dandyala D. S. (2024). Integrating Zero Trust Architecture with Service Mesh for Enhanced Cloud Security in DevOps Workflows. International Journal of Computer and Information System (IJCIS), vol 05(04), pp. 331 - 336. doi: https://ijcis.net/index.php/ijcis/index
DuPont Q. & Fidler B. (2016). Edge Cryptography and the Codevelopment of Computer Networks and Cybersecurity. IEEE Annals of the History of Computing, vol 38(4), pp. 55-73. doi:10.1109/MAHC.2016.49
Feng Y. et al. (2022). Blockchain-empowered secure federated learning system: Architecture and applications. Computer Communications, vol 196, pp 55-65. doi:https://doi.org/10.1016/j.comcom.2022.09.008
Ferretti L. et al. (2021). Survivable zero trust for cloud computing environments. Computers & Security, vol 110(102419). doi:https://doi.org/10.1016/j.cose.2021.102419
Ganapati S. et al. (2023). Evolution of Cybersecurity Concerns: A Systematic Literature Review. Proceedings of the 24th Annual International Conference on Digital Government Research, pp. 90 - 97. doi:https://doi.org/10.1145/3598469.3598478
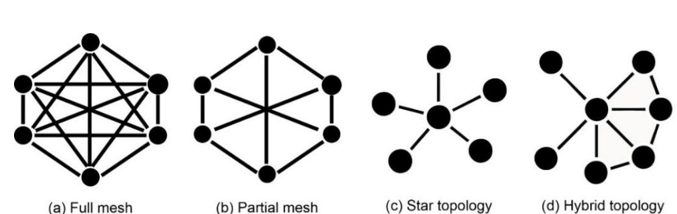
Garcia L. et al. (2025). Compliant and Seamless Hybrid (Star and Mesh) Network Topology Coexistence for LoRaWAN: A Proof of Concept. Applied Sciences, vol 15(7), pages 1-25. doi:https://doi.org/10.3390/app15073487
Gartner Inc. (2025, June 25th). Cybersecurity Mesh. Retrieved from In Gartner IT Glossary: https://www.gartner.com/en/information-technology/glossary/cybersecurity-mesh
Gartner Inc. (2025). Secure Access Service Edge (SASE). Retrieved June 25, 2025, from Gartner: https://www.gartner.com/en/information-technology/glossary/secure-access-service-edge-sase
Gartner Inc. (2020, October 19). Gartner. (Gartner Inc) Retrieved June 24, 2025, from Newsroom: Press Releases: https://www.gartner.com.au/en/newsroom/press-releases/2020-10-19-gartner-identifies-the-top-strategic-technology-trends-for-2021
Gartner Inc. (2023, January). Cybersecurity Mesh Architecture (CSMA). Retrieved June 25th, 2025, from Gartner: https://www.gartner.com/peer-community/oneminuteinsights/omi-cybersecurity-mesh-architecture-csma-guf
Infosec Institute. (2014, May 13th). A History of Malware: Part One, 1949-1988. (Cengage Learning) Retrieved July 10th, 2025, from Infosec: Malware analysis: https://www.infosecinstitute.com/resources/malware-analysis/history-malware-part-one-1949-1988/
Jianli P. et al. (2018). Cybersecurity Challenges and Opportunities in the New "Edge Computing + IoT" World. CODASPY '18: Eighth ACM Conference on Data and Application Security and Privacy (pp. Pages 29 - 32). New York, United States: Association for Computing Machinery (ACM). doi: https://doi.org/10.1145/3180465.3180470
Ju L. et al. (2024). Enhancing real-time intrusion detection and secure key distribution using multi-model machine learning approach for mitigating confidentiality threats. Internet of Things, 28(101377). doi:https://doi.org/10.1016/j.iot.2024.101377
Kessler C. G. and Pritsky T. N. (2009). Network Topologies, Protocols, and Design. In W. E. Bosworth S., Computer Security Handbook (5th Edition ed.). Wiley.
Kotha R. N. (2020). Network Segmentation as a Defense Mechanism for Securing Enterprise Networks. Turkish Journal of Computer and Mathematics Education (TURCOMAT), vol 11(3), Pages 3023-3030. doi:https://doi.org/10.61841/turcomat.v11i3.14942
Liu C. et al. (2024). Dissecting zero trust: research landscape and its implementation in IoT. Cybersecurity, vol 7(20). doi:https://doi.org/10.1186/s42400-024-00212-0
Mahmood Z. & Jusas V. (2022). Blockchain-Enabled: Multi-Layered Security Federated Learning Platform for Preserving Data Privacy. Electronics: Networks, vol 11(10). doi:https://doi.org/10.3390/electronics11101624
Mampilly A. J. & Midhunchakkaravarthy D. (2025). Cybersecurity Mesh Architecture: A Framework for Enhanced Compatibility and Security in the Digital Age. In S.
C. Pon , N. Sehgal, S. Ruhela, & N. Rizvi (Ed.), International Conference on Innovation, Sustainability, and Applied Sciences. ICISAS 2023. Signals and Communication Technology (pp. pp 441-445). Springer, Cham. doi: https://doi.org/10.1007/978-3-031-68952-9_58
Matthews T. (2022, January 1st). Creeper: The World’s First Computer Virus. Retrieved July 10th, 2025, from Exabeam: https://www.exabeam.com/blog/infosec-trends/creeper-the-worlds-first-computer-virus/
Munoz A., Sanchez-Cid F., El Khoury P. . et al. (2008). XACML as a Security and Dependability Pattern for Access Control in AmI environments. Developing Ambient Intelligence (pp. Pages 143 -155). Paris: Springer. doi: https://doi.org/10.1007/978-2-287-78544-3_14
Ogunbadejo M. D. et al. (2025). Overview of Zero Trust Architecture Trend and Advancement in Information Security. Journal of Information Engineering and Applications (JIEA), vol 15(1), pp. 21- 30. doi:https://10.7176/JIEA/15-1-03
Orabi M. M., Emam O. & Fahmy H. (2025). Adapting security and decentralized knowledge enhancement in federated learning using blockchain technology: literature review. Journal of Big Date, vol 12(55). doi:https://doi.org/10.1186/s40537-025-01099-5
Pallewatta S. and Babar A. M. (2024). Towards Secure Management of Edge-Cloud IoT Microservices using Policy as Code. (M. Galster, P. Scandurra, T. Mikkonen, P. O. Antonino, E. Y. Nakagawa, & E. Navarro, Eds.) Software Architecture. ECSA 2024. Lecture Notes in Computer Science, vol 14889, Pages 1-16. doi:https://doi.org/10.1007/978-3-031-70797-1_18
Parast K. F. et al. (2022). Cloud computing security: A survey of service-based models. Computers & Security, 114(102580). doi:https://doi.org/10.1016/j.cose.2021.102580
Punia A. et al. (2024). A systematic review on blockchain-based access control controls systems in cloud environment. Journal of Cloud Computing, vol 13(146), pp. 1-37. doi: https://doi.org/10.1186/s13677-024-00697-7
Qammar A. et al. (2023). Securing federated learning with blockchain: a systematic literature review. Artificial Intelligence Review, vol 56, pp 3951 -3985. doi:https://doi.org/10.1007/s10462-022-10271-9
Ramos-Cruz, B., Andreu-Perez, J., & Martinez, L. (2024). The cybersecurity mesh: A comprehensive survey of involved artificial intelligence methods, cryptographic protocols and challenges for future research. Neurocomputing, vol 581(127427), pages 1-33. doi:https://doi.org/10.1016/j.neucom.2024.127427
Reddy V. R et al. (2024). Adaptive Vulnerability Matching Assessment: A Holistic Approach for Cyber security Resilience. Iternational Journal For Research in Applied Science and Engineering Technology (IJRASET), 2(3), pages 46 - 51. doi: https://doi.org/10.22214/ijraset.2024.59554
Ren Y., Wang Z., Sharma K. P. et al. (2025). Zero Trust Networks: Evolution and Application from Concept to Practice. Computers, Materials & Continua, vol 82(2), Pages 1593-1613. doi: https://doi.org/10.32604/cmc.2025.059170
Repetto M. et al. (2021). An Autonomous Cybersecurity Framework for Next-generation Digital Service Chains. Journal of Networks and Systems Management, vol 29(37), pages 1-34. doi: https://doi.org/10.1007/s10922-021-09607-7
Rose S. et al. (2020). Zero Trust Architecture. NIST Special Publication 800-207, pp 1-50. doi:https://doi.org/10.6028/NIST.SP.800-207
Saqid M. et al. (2025). Adaptive Security Policy Management in Cloud Environments Using Reinforcement Learning. Cryptography and Security. doi:https://doi.org/10.48550/arXiv.2505.08837
Sarhan M. et al. (2022). HBFL: A hierarchical blockchain-based federated learning framework for collaborative IoT intrusion detection. Computers and Electrical Engineering, vol 103(108379). doi:https://doi.org/10.1016/j.compeleceng.2022.108379
Theodoropoulos T. et al. (2023). Security in Cloud-Native Services: A Survey. Journal of Cybersecurity and Privacy, vol 3(4), pp 758 - 793. doi: https://doi.org/10.3390/jcp3040034
Tim M. et al. (2009). Cloud Security and Privacy: An Enterprise perspective on Risks and Compliance (Vol. First edition). USA: O'Reilly Media Inc.
Unal D. et al. (2021). Integration of federated machine learning and blockchain for the provision of secure big data analytics for Internet of Things. Computers & Security, vol 109(102393). doi:https://doi.org/10.1016/j.cose.2021.102393
United States Cybersecurity Institute. (2024). Cybersecurity Mesh Architecture (CSMA): An Overview. Retrieved June 28th, 2025, from https://www.uscsinstitute.org/cybersecurity-insights/blog/cybersecurity-mesh-architecture-an-overview
Walling S. (2020). A Comprehensive Review on Cloud Computing and Cloud Security Issues. International Journal of Scientific Research in Computer Science, Engineering and Information Technology (IJSRCSEIT), vol 6(4), Pages 483-490. doi: https://doi.org/10.32628/CSEIT206489
Widowati U. F. (2025). Cybersecurity Mesh and Edge Computing on the Analytics Platform of the Indonesian Telecommunications Industry. International Journal of Management Science and Information Technology (IJMSIT), vol 5(1), pages 183 - 191. doi:https://doi.org/10.35870/ijmsit.v5i1.3845
Xi N. et al. (2023). Decentralized access control for secure microservices cooperation with blockchain. ISA Transactions, 141, pages 44-51. doi:https://doi.org/10.1016/j.isatra.2023.07.018
Yang J., Zhang W., Guo Z., & Gao Z. (2023). TrustDFL: A Blockchain-Based Verifiable and Trusty Decentralized Federated Learning Framework. Electronics, vol 13(1). doi:https://doi.org/10.3390/electronics13010086
Yongjun R. et al. (2025). Zero Trust Networks: Evolution and Application from Concept to Practice. Computers, Materials and Continua, vol 82(2), Pages 1593-1613. doi:https://doi.org/10.32604/cmc.2025.059170
Zhang J. et al. (2024). CSFL: Cooperative Security Aware Federated Learning Model Using The Blockchain. The Computer Journal, vol 67(4), pp 1298-1308. doi:https://doi.org/10.1093/comjnl/bxad060
Zheng Y. et al. (2022). Dynamic defenses in cyber security: Techniques, methods and challenges. Digital Communications and Networks, vol 8(4), Pages 422-435. doi:https://doi.org/10.1016/j.dcan.2021.07.006
Downloads
Published
Issue
Section
Categories
License
Copyright (c) 2026 Suleman Idris Zubairu, Rabiu Ibrahim Suleiman, Aliyu Abdullahi

This work is licensed under a Creative Commons Attribution 4.0 International License.