ADAPTIVE RISK-BASED MULTI-LAYER AUTHENTICATION FRAMEWORK FOR SECURE ONLINE BANKING SYSTEMS
DOI:
https://doi.org/10.33003/fjs-2026-1004-4870Keywords:
Adaptive authentication, Cybersecurity, Fraud detection, Multi-factor authentication, Online banking security, Risk-based authenticationAbstract
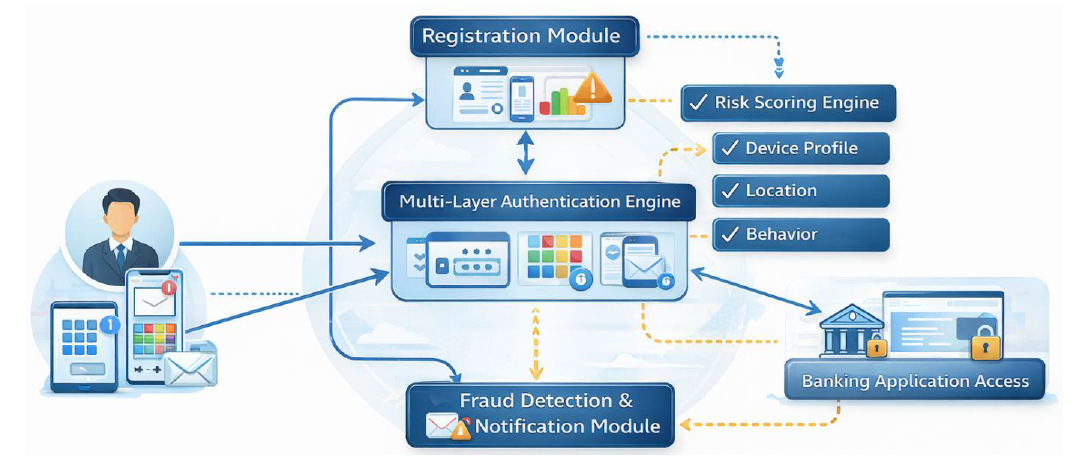
Digital banking services have grown rapidly, increasing exposure to credential theft, phishing, replay attacks, and account takeover fraud. Traditional, single-factor, and static multi-factor authentication systems are still susceptible in the event that attackers breach one or more levels of authentication. This paper presents and experimentally confirms an adaptive risk-based multi-layer authentication system adapted to an online banking context. The model integrates knowledge-based verification (PIN), recognition-based graphical authentication, possession-based one-time password (OTP), and a dynamic risk-scoring engine that adjusts authentication strictness based on contextual indicators such as login location, device profile, and behavioral anomalies. A probabilistic security model is designed to measure the likelihood of attack success, measured by independent authentication layers. The framework was tested in the web-based prototype environment and tested with 120 participants who underwent 500 total authentication attempts, and with simulated adversarial conditions. False Acceptance Rate (FAR), False Rejection Rate (FRR), Equal Error rate (EER), Area Under the ROC Curve (AUC), Precision, recall, and response time were used to measure the performance. The presented adaptive framework demonstrated a high authentication rate of 98.9, FAR of 0.7, FRR of 2.6, and EER of 1.65, which is considerably higher than single-factor and fixed two-factor baselines. The ROC analysis had an AUC equal to 0.991, which implies that it has a high discrimination ability. These results indicate that risk-adaptive authentication has a higher resilience to fraud and can still be operated effectively.
References
Aloul, F., Zahidi, S., & El-Hajj, W. (2009, May). Two factor authentication using mobile phones. In 2009 IEEE/ACS international conference on computer systems and applications (pp. 641-644). IEEE.
Anwar, N. M., Ahmad, S. S. S., Kausar, N., Stević, Ž., & Gaba, Y. U. (2025). Multiple biometric authentication for online banking system based on multiple fuzzy approach. Scientific Reports, 15(1), 32824.
Bhargav-Spantzel, A., Squicciarini, A., & Bertino, E. (2007). Establishing and protecting digital identity in federation systems. Journal of Computer Security, 14(3), 269–300.
Biddle, R., Chiasson, S., & Van Oorschot, P. (2012). Graphical passwords: Learning from the first twelve years. ACM Computing Surveys, 44(4), 1–41.
Bonneau, J., Herley, C., Van Oorschot, P. C., & Stajano, F. (2012, May). The quest to replace passwords: A framework for comparative evaluation of web authentication schemes. In 2012 IEEE symposium on security and privacy (pp. 553-567). IEEE.
Carjuman, N., Fook, L. C., & Hlaing, Z. C. (2025, November). Enhanced MFA Framework Against Modern Security Threats. In Proceedings of the 2025 10th International Conference on Cloud Computing and Internet of Things (pp. 148-155).
Claessens, J., Dem, V., De Cock, D., Preneel, B., & Vandewalle, J. (2002). On the security of today’s online electronic banking systems. Computers & Security, 21(3), 253–265.
Das, A., Bonneau, J., Caesar, M., Borisov, N., & Wang, X. (2014, February). The tangled web of password reuse. In Network and Distributed System Security Symposium (NDSS) (Vol. 14, No. 2014, pp. 23-26).
Florêncio, D., & Herley, C. (2007). A large-scale study of web password habits. Proceedings of the World Wide Web Conference, 657–666.
Freeman, D., Jain, S., Dürmuth, M., Biggio, B., & Giacinto, G. (2016, February). Who Are You? A Statistical Approach to Measuring User Authenticity. In Network and Distributed System Security Symposium (NDSS) (Vol. 16, pp. 21-24).
Ghiyamipour, F. (2021). Secure graphical password based on cued click points using fuzzy logic. Security and Privacy, 4(2), e140.
Grassi, P. A., Garcia, M. E., & Fenton, J. L. (2017). Digital identity guidelines: Authentication and lifecycle management (NIST SP 800-63B). National Institute of Standards and Technology.NIST special publication, 800, 63-3.
Herley, C., & Van Oorschot, P. (2012). A research agenda acknowledging the persistence of passwords. IEEE Security & Privacy, 10(1), 28–36.
Jain, A., Ross, A., & Pankanti, S. (2006). Biometrics: A tool for information security. IEEE Transactions on Information Forensics and Security, 1(2), 125–143.
Kandula, S. R., Kassetty, N., ALANG, K. S., & Pandey, P. (2024). Context-aware multi-factor authentication in zero trust architecture: Enhancing security through adaptive authentication. International Journal of Global Innovations and Solutions (IJGIS).
Oduguwa, T., & Arabo, A. (2024). Passwordless authentication using cryptography, steganography, and biometrics. Journal of Cybersecurity and Privacy. 4(2), 278-297.
Ometov, A., Bezzateev, S., Mäkitalo, N., et al. (2018). Multi-factor authentication: A survey. Cryptography, 2(1), 1–37.
Podapati, V. H., Nigam, D., & Das, S. (2025, July). SoK: a systematic review of context-and behavior-aware adaptive authentication in mobile environments. In International Symposium on Human Aspects of Information Security and Assurance (pp. 406-419). Cham: Springer Nature Switzerland.
Raghu, N., Bhat, R., Nambiar, P. R., Shetty, G. S., & DB, A. K. (2025). Blockchain-enhanced GAN image encryption scheme for cloud computing. In Intelligent Systems and IoT Applications in Clinical Health (pp. 367-392). IGI Global.
Saadi, Z. M., Sadiq, A. T., Akif, O. Z., & Farhan, A. K. (2024). Security vulnerabilities and protective strategies for graphical passwords. Electronics, 13(15), 3042
Traore, I., Woungang, I., Nakkabi, Y., Obaidat, M. S., Ahmed, A. A. E., & Khalilian, B. (2012). Dynamic sample size detection in learning command line sequence for continuous authentication. IEEE Transactions on Systems, Man, and Cybernetics, Part B (Cybernetics), 42(5), 1343-1356.
Wiedenbeck, S., Waters, J., Birget, J., Brodskiy, A., & Memon, N. (2005). PassPoints: Design and longitudinal evaluation of a graphical password system. International Journal of Human-Computer Studies, 63(1–2), 102–127.
Downloads
Published
Issue
Section
Categories
License
Copyright (c) 2026 Jumoke Soyemi, Mudasiru Hammed, Olugbenga Babajide Soyemi

This work is licensed under a Creative Commons Attribution 4.0 International License.